MOBILE PHONE FORENSIC SERVICES IOS AND ANDROID
Technogeek Mobile Phone Forensics
The prevalence of mobile phone forensics has increased as smartphone devices improve in terms of functionality, data storage, and all-around capabilities. Our digital forensic investigators work all throughout Brisbane and are experts in mobile phone investigations. When we recover electronic data from mobile devices, we retain, extract, analyse, and report it for use in criminal, civil, business, and legal aid cases.
Mobile phone forensic services involve the examination, analysis, and extraction of digital evidence from mobile devices such as smartphones and tablets. This process is typically conducted for legal, investigative, or security purposes. Mobile phone forensics can reveal valuable information about a device's usage history, communications, applications, and stored data.
From the first point of contact through the end of any digital forensic investigation, our Client's Confidentiality is of the utmost concern, and all interaction is handled with caution.
Targeted research is performed by our Technogeek Digital Forensics specialists to unearth a variety of data that may be crucial to a case. Web and user activity, access and update dates, email history, and printing, copying, and deleting history are a few examples.
What are the common techniques used in mobile device forensics?
↻ MOBILE FORENSIC:
↻ DATA SERVICES:
How long does phone forensics take?
Technogeek specialises in recovering missing
or deleted texts on iOS and Android devices
Here's an overview of what these services entail:
Data Extraction: Mobile forensics experts use specialized tools and techniques to extract data from mobile devices. This includes retrieving text messages, call logs, contacts, photos, videos, app data, browsing history, and more.
Deleted Data Recovery: Forensic experts can often recover deleted data that is still present on the device's storage. This can provide valuable insights, especially in criminal investigations.
Forensic Imaging: A bit-by-bit copy of the device's storage is created, known as a forensic image. This ensures that the original data is preserved and can be analyzed without altering the source device.
Data Analysis: Extracted data is carefully analyzed to reconstruct the timeline of events, communications, and interactions on the device. This can help in understanding the user's activities and intentions.
Password and Encryption Handling: Mobile devices are often protected with passwords, PINs, or encryption. Forensics experts may employ various techniques to bypass or crack these protections, legally and ethically, to access the device's contents.
App Data Examination: Many mobile apps store sensitive information, and forensics professionals can uncover data from messaging apps, social media, email clients, and more.
Technogeek offers top-notch computer forensics
services for iOS and Android devices in Kallangur.
Location Data Analysis: Mobile devices often store location information through GPS and other means. Analyzing this data can provide insights into a person's movements.
Call Detail Analysis: Call logs and associated metadata can be used to understand communication patterns and connections between individuals.
Expert Testimony: In legal cases, mobile forensics experts may be called upon to provide expert testimony in court, explaining our findings and the significance of the digital evidence.
Data Integrity and Chain of Custody: Proper procedures are followed to ensure the integrity of the evidence and maintain a clear chain of custody, crucial for the evidence's admissibility in legal proceedings.
Malware and Security Analysis: Mobile forensics can also involve identifying and analyzing malware, potentially providing insights into security breaches or cyberattacks.
Remote Forensics: In some cases, remote mobile forensics might be performed, allowing experts to analyze a device's data without physically having access to it. This could involve cloud-based backups or remote device management tools.
What can forensics see on iPhone?
Technogeek is your go-to for iOS and Android forensics in Kallangur.
Recovery of deleted or lost data.
Summary of mobile internet usage.
Production of photographs, videos, messages and call lists.
Determine location of a phone at a specific time and date.
It's important to note that mobile phone forensic services must be conducted with strict adherence to legal and ethical guidelines. Privacy considerations, data protection laws, and proper authorisation are critical aspects of any mobile phone forensic investigation.
What type of evidence can be extracted from a mobile device?
Need an Insurance Report?
Spilled your coffee? Dropped your Laptop? Power Surge? Get our fast, Our insurance reports to allow you to file your claim fast!

Your Tech Fix-It Repairer!
From windows software updates causing issues to hardware repairs and fixes, we can help solve your computer tech troubles with ease.

Full Dust Clean Services:
Breathe easy! Laptop or Desktop Computers. We banish dust bunnies and grime, keeping your computer running cool and efficient.

Complete Tune Up Services:
Is your laptop or computer performing slowly? Our 12 point Tune-up service offers a peak performance boost. It is just like a fresh start for your pc!

Email Us
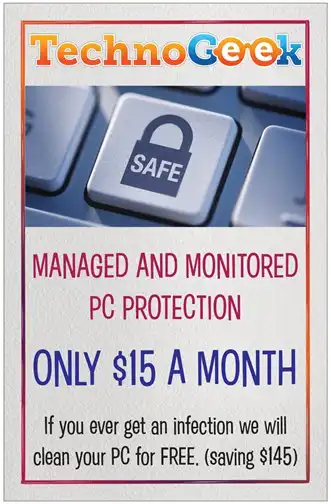
FIXED FEE WORKSHOP & REMOTE SERVICES
Office Address
13 Stokes Street North Lakes
Office Hours
WEEKDAYS: 8am to 6:30pm
SAT: 9am to 12pm
CLOSED SUNDAYS & PUBLIC HOLIDAYS
